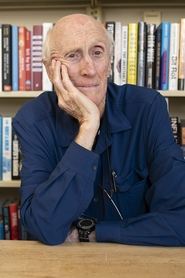
Hackers: Wizards of the Electronic Age(1984)
All interviews in this documentary were shot over a long weekend at a 1984 hacker conference by the Whole Earth Catalog editors Stewart Brand and Kevin Kelley in Sausalito, California. The event itself (the hacker conference) was inspired by Steven Levy's classic book "Hackers - Heroes of the Computer Revolution"
Movie: Hackers: Wizards of the Electronic Age
Top 7 Billed Cast

Hackers: Wizards of the Electronic Age
HomePage
Overview
All interviews in this documentary were shot over a long weekend at a 1984 hacker conference by the Whole Earth Catalog editors Stewart Brand and Kevin Kelley in Sausalito, California. The event itself (the hacker conference) was inspired by Steven Levy's classic book "Hackers - Heroes of the Computer Revolution"
Release Date
1984-01-01
Average
7
Rating:
3.5 startsTagline
Genres
Languages:
EnglishKeywords
Recommendations Movies
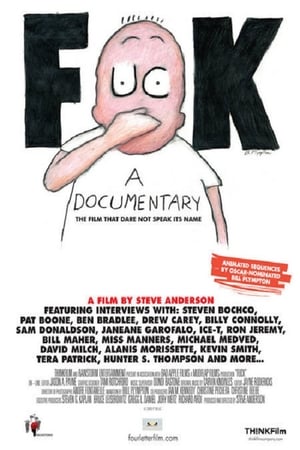
 6.4
6.4Louis Theroux: Twilight of the Porn Stars(en)
In 1997, Louis Theroux made a documentary about the world of male porn performers in Los Angeles. 15 years later, he returns to find a business struggling with the deluge of free porn on the internet. Louis revisits some of the original programme's contributors as well as meeting the latest crop of porn performers dreaming of porn stardom.
 7.8
7.8The Godfather Family: A Look Inside(en)
A documentary on the making of the three Godfather films, with interviews and recollections from the film makers and cast. This feature also includes the original screen tests of some of the actors for "The Godfather" film, and some candid moments on the set of "The Godfather: Part III."
 7.1
7.1Making The Witcher(en)
Journey into the extraordinary world of "The Witcher" — from casting the roles to Jaskier's catchy song — in this behind-the-scenes look at the series.
 6.1
6.1Takedown(en)
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...
 7.3
7.3Zero Days(en)
Alex Gibney explores the phenomenon of Stuxnet, a self-replicating computer virus discovered in 2010 by international IT experts. Evidently commissioned by the US and Israeli governments, this malware was designed to specifically sabotage Iran’s nuclear programme. However, the complex computer worm ended up not only infecting its intended target but also spreading uncontrollably.
 7.2
7.24 Little Girls(en)
On September 15, 1963, a bomb destroyed a black church in Birmingham, Alabama, killing four young girls who were there for Sunday school. It was a crime that shocked the nation--and a defining moment in the history of the civil-rights movement. Spike Lee re-examines the full story of the bombing, including a revealing interview with former Alabama Governor George Wallace.
 7.1
7.1We Are Legion: The Story of the Hacktivists(en)
Takes us inside the world of Anonymous, the radical "hacktivist" collective that has redefined civil disobedience for the digital age. The film explores early hacktivist groups like Cult of the Dead Cow and Electronic Disturbance Theater, then moves to Anonymous' raucous beginnings on the website 4chan. Through interviews with current members, people recently returned from prison or facing trial, writers, academics, activists and major players in various "raids," the documentary traces Anonymous’ evolution from merry pranksters to a full-blown movement with a global reach, the most transformative civil disobedience of our time.
 7.8
7.8Interstellar: Nolan's Odyssey(en)
A look behind the lens of Christopher Nolan's space epic.
 7.1
7.1Marvel Studios Assembled: The Making of Hawkeye(en)
Join the likes of Jeremy Renner, Hailee Steinfeld, Florence Pugh, and Vincent D’Onofrio as they reveal how Marvel Studios’ “Hawkeye” was conceived and created. Witness firsthand what it took to pull off the show’s pulse-pounding action set pieces, and discover how iconic characters from the pages of Marvel Comics such as Kate Bishop were adapted and brought to life for the six-episode series.
 7.1
7.1The Summers of It - Chapter Two: It Ends(en)
This documentary focuses on the actors and their journey over two summers to create the remake to the original IT, by Stephen King. The documentary originally released as bonus material, bundled with IT: Chapter Two.
 6.8
6.8Spider-Man: All Roads Lead to No Way Home(en)
JB Smoove and Martin Starr host a celebration of 20 years of "Spider-Man" movies, from the Sam Raimi trilogy to Marc Webb's movies and the trio from Jon Watts.
 6.2
6.2Evil Influencer: The Jodi Hildebrandt Story(en)
Unravel the case of Utah therapist Jodi Hildebrandt, whose child abuse arrest with parenting YouTuber Ruby Franke exposed a twisted tale of manipulation.
 7.2
7.2Seven Up!(en)
A group of British children aged 7 from widely ranging backgrounds are interviewed about a range of subjects. The filmmakers plan to re-interview them at 7 year intervals to track how their lives and attitudes change as they age.
 6.1
6.1Naqoyqatsi(en)
A visual montage portrait of our contemporary world dominated by globalized technology and violence.
 6.8
6.8And the Oscar Goes To...(en)
The story of the gold-plated statuette that became the film industry's most coveted prize, AND THE OSCAR GOES TO... traces the history of the Academy itself, which began in 1927 when Louis B. Mayer, then head of MGM, led other prominent members of the industry in forming this professional honorary organization. Two years later the Academy began bestowing awards, which were nicknamed "Oscar," and quickly came to represent the pinnacle of cinematic achievement.
 8.4
8.4No Half Measures: Creating the Final Season of Breaking Bad(en)
A documentary about the making of season five of the acclaimed AMC series Breaking Bad.
 6.4
6.4Champs(en)
A documentary about the sport of boxing, as seen through the eyes of champions Mike Tyson, Evander Holyfield and Bernard Hopkins.
 6.5
6.5Downloaded(en)
A documentary that explores the downloading revolution; the kids that created it, the bands and the businesses that were affected by it, and its impact on the world at large.
 7.2
7.2Louis Theroux: Louis and the Nazis(en)
Louis Theroux travels to California to meet the man dubbed "the most dangerous racist in America"; Tom Metzger. Louis meets him, his family and his publicity manager as well as following him to skinhead rallies and on a visit to Mexico.
Similar Movies
 0.0
0.0Russia's Cyber Army(ru)
For years now, the Kremlin has been systematically trying to use well-trained hackers for its own benefit. In exchange for freedom and protection, they do the dirty work of the state, interfering in other countries’ elections and penetrating government networks. Just how dangerous is Russia’s cyber army?
 5.2
5.2The New Radical(en)
Uncompromising millennial radicals from the United States and the United Kingdom attack the system through dangerous technological means, which evolves into a high-stakes game with world authorities in the midst of a dramatically changing political landscape.
 8.1
8.1The KGB, the Computer and Me(en)
In 1986, astronomer turned computer scientist Clifford Stoll had just started working on a computer system at the Lawrence Berkeley Laboratory when he noticed a 75-cent discrepancy between the charges printed by two accounting programs responsible for charging people for machine use. Intrigued, he deduced that the system was being hacked, and he determined to find the culprit. This is the re-enactment of how he tracked down KGB cracker Markus Hess through the Ethernet to Hannover, Germany.
 6.5
6.5Cyberbunker: The Criminal Underworld(de)
This documentary reveals how a group of hackers powered the darkest corners of the internet from a Cold War-era bunker in a quiet German tourist town.
 6.4
6.4In the Realm of the Hackers(en)
In The Realm of the Hackers is a documentary about the prominent hacker community, centered in Melbourne, Australia in the late 80's to early 1990. The storyline is centered around the Australian teenagers going by the hacker names "Electron" and "Phoenix", who were members of an elite computer hacking group called The Realm and hacked into some of the most secure computer networks in the world, including those of the US Naval Research Laboratory, Lawrence Livermore National Laboratory, a government lab charged with the security of the US nuclear stockpile, and NASA.
 7.0
7.0Freedom Downtime(en)
A feature-length documentary about the Free Kevin movement and the hacker world.
 7.0
7.0Revolution OS(en)
REVOLUTION OS tells the inside story of the hackers who rebelled against the proprietary software model and Microsoft to create GNU/Linux and the Open Source movement.
 0.0
0.0Guardians of the New World(en)
Guardians of the New World introduces us to the world of hacker culture. Emerging from the 70’s counterculture around conceptions of personal freedom, decentralisation of power and sharing, hacking really came to prominence with the emergence of the Internet as a ubiquitous public forum from the late 90’s onwards.
 5.3
5.3Cabin Pressure(en)
A fully automated commercial jetliner is prepared to make its maiden voyage. Without an on-flight pilot, the craft relies on satellite linking for its course. But when the plane suddenly deviates from its determined route and establishes a circular pattern over Seattle, it becomes evident that the craft has been hijacked by a disgruntled former airline employee who has hacked into the flight's computer system from his apartment, somewhere in the United States. Now, a former discredited Navy pilot and an oddball technician must race against the clock to find where the angry employee is, and regain control of the plane before it crashes into the city.
 7.0
7.0Code 2600(en)
CODE 2600 documents the rise of the Information Technology Age as told through the events and people who helped build and manipulate it.
 7.1
7.1We Are Legion: The Story of the Hacktivists(en)
Takes us inside the world of Anonymous, the radical "hacktivist" collective that has redefined civil disobedience for the digital age. The film explores early hacktivist groups like Cult of the Dead Cow and Electronic Disturbance Theater, then moves to Anonymous' raucous beginnings on the website 4chan. Through interviews with current members, people recently returned from prison or facing trial, writers, academics, activists and major players in various "raids," the documentary traces Anonymous’ evolution from merry pranksters to a full-blown movement with a global reach, the most transformative civil disobedience of our time.
 0.0
0.0My Sextortion Diary(ca)
Pati, a young film producer, is fighting to carve out a professional career in the film industry. It is May 2019 when her laptop is stolen during a business trip in Madrid. Two months after, an anonymous Hacker accesses all the stored data in the stolen device and finds three very private photos of Pati. He threatens that if he doesn’t receive $2,400 he will mass-mail the pictures to all her work contacts in order to ruin her professional reputation. The shame, anger and distress caused by the ineffectiveness of the legal forces lead Pati to set out on her own investigation to stop the Hacker and regain control and power over her privacy.
 7.8
7.8Hackers: Outlaws and Angels(en)
This program reveals the daily battle between the Internet’s outlaws and the hackers who oppose them by warding off system attacks, training IT professionals and police officers, and watching cyberspace for signs of imminent infowar. Through interviews with frontline personnel from the Department of Defense, NYPD’s computer crime squad, private detective firm Kroll Associates, X-Force Threat Analysis Service, and several notorious crackers, the program provides penetrating insights into the millions of hack attacks that occur annually in the U.S.—including one that affected the phone bills of millions and another that left confidential details of the B-1 stealth bomber in the hands of teenagers. The liabilities of wireless networks, the Code Red worm, and online movie piracy are also discussed. A Discovery Channel Production. (51 minutes)
 7.0
7.0Computer assault(es)
Each of the members of a group of hackers is willing to fight against system. Their messages and attacks are political, socially demmanding but also playful. Each of them have reasons to have moved to that virtual side, where they can be who they can't in real life. However, the sudden implication of authorities (pressed by goverment to be tougher against hackers)and of a wise and dangerous cracker will cause a turn in their crusade. Will they use the enemy's means or their ideological motivations imply a respect for law and human life?
 9.0
9.0All Creatures Welcome(de)
All Creatures Welcome explores the world of hackers and nerds at the events of the Chaos Computer Club, Europe's largest hacker association. The film dispels common clichés and draws a utopian picture of a possible society in the digital age.
 6.4
6.4Cyberbully(en)
A chilling real-time thriller featuring a teenager, Casey, battling with an anonymous cyber-stalker.
 6.5
6.5Nackt. Das Netz vergisst nie.(de)
16-year-old Lara takes nude photos for her boyfriend, which soon flood social media. Lara's phone has been hacked, the photos published, and she's being blackmailed.
 6.8
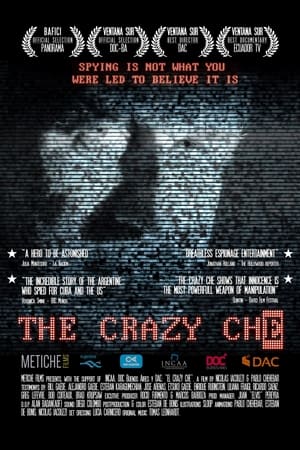
6.8The Crazy Che(es)
The incredible story of Bill Gaede, an Argentinian engineer, programmer… and Cold War spy.
 8.0
8.0Tracking Russian Hackers(fr)
Amid the growing threat of cyberattacks from Russian hackers, this film dives into their origins, motives, and the dangers they pose to their targets.
 8.0
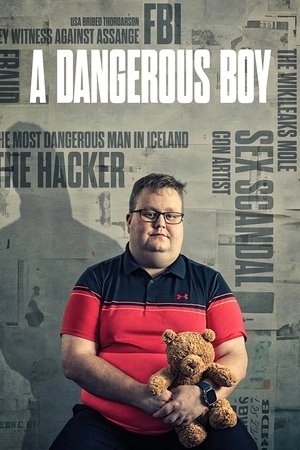
8.0A Dangerous Boy(en)
Sigurdur Thordarson, known as Siggi, becomes a hacker at 12, exposing Icelandic bank corruption at 14. Branded the "teenage whistleblower," he joins WikiLeaks in 2010, mentored by Julian Assange. Siggi leaks globally, but clashes with Assange, prompting him to spy for the FBI at 18. This tale weaves paranoia, hacking, and friendship, portraying Siggi's turbulent journey from trust to betrayal, revealing a heart-wrenching coming-of-age narrative.