The Takeover(2022)
Self-proclaimed ethical hacker Mel Bandison's life is turned upside down when she stops a data breach on a high-tech self-driving bus that also happens to shut down an international criminal network. She then becomes a target and is framed with a deepfake video that “shows” that she murders someone.

Movie: The Takeover
Top 10 Billed Cast
Robin
Video Trailer The Takeover
Recommendations Movies
 7.1
7.1The System(en)
When a young soldier, newly returned from war, gets caught up in a drug bust, he is recruited by the authorities to go undercover in a notoriously dangerous prison in order to figure out what is really going on.
 6.5
6.5The Last Days of American Crime(en)
In the not-too-distant future, as a final response to crime and terrorism, the U.S. government plans to broadcast a signal that will make it impossible for anyone to knowingly break the law.
 6.2
6.2The Island(en)
When his brother is killed, LAPD officer Mark leaves the city to return to the island he grew up on. Seeking answers and ultimately vengeance, he soon finds himself in a bloody battle with the corrupt tycoon who's taken over the island paradise.
 6.6
6.6Trap House(en)
An undercover DEA agent and his partner embark on a game of cat and mouse with an audacious, and surprising group of thieves – their own rebellious teenagers, who have begun robbing from a dangerous cartel, using their parents' tactics and top-secret intel to do it.
 6.7
6.7Kill 'em All 2(en)
Phillip and Suzanne are retired from the spy game, living peacefully off the grid. That's until their whereabouts are discovered by Vlad, the vengeful brother of their target from the first film.
 5.9
5.9White Elephant(en)
An ex-marine enforcer must battle his conscience and code of honor when he is forced to do things for the mob.
 5.9
5.9S.W.A.T.: Under Siege(en)
When a D.E.A. and S.W.A.T. cartel takedown ends in a shootout, S.W.A.T. Agent Travis Hall seizes a mysterious prisoner taking him into custody. Before long, the S.W.A.T. compound is under siege by wave-after-wave of assault teams attempting to recover the prisoner known as “The Scorpion” for the tattoo blazed across his back. When Travis discovers that his prisoner is a Secret Ops double agent planted within the cartel, it’s up to him and his expert S.W.A.T. team to keep “The Scorpion” and his billion dollar secrets safe.
 6.3
6.3Icefall(en)
A young Indigenous game warden arrests an infamous poacher only to discover that the poacher knows the location of a plane carrying millions of dollars that has crashed in a frozen lake. When a group of criminals and dirty cops are alerted to the poacher’s whereabouts, the warden and the poacher team up to fight back and escape across the treacherous lake before the ice melts.
 6.5
6.5Hellhound(en)
Ready to leave his profession behind, Loreno, an assassin, lends help to an old friend, Cetan, and taking one last job in Thailand seeking out a local kingpin. A lapse in judgment means Loreno crosses paths with old colleague Paul.
 6.9
6.9Hunting Season(en)
When a reclusive survivalist and his daughter rescue a mysterious, wounded woman from a river, they become entangled in a deadly web of violence and revenge, forcing them to confront a brutal criminal to survive.
 6.0
6.0God Is a Bullet(en)
Vice detective Bob Hightower finds his ex-wife murdered and daughter kidnapped by a cult. Frustrated by the botched official investigations, he quits the force and infiltrates the cult to hunt down the leader with the help of the cult’s only female victim escapee, Case Hardin.
 6.2
6.2Stretch(en)
A hard-luck limo driver struggling to go straight and pay off a debt to his bookie takes on a job with a crazed passenger whose sought-after ledger implicates some seriously dangerous criminals.
 5.8
5.8Bring Him to Me(en)
Under orders from a ruthless crime boss, a getaway driver must battle his conscience and drive an unsuspecting crew member to an ambush execution. There is a long drive ahead.
 6.1
6.1Black Site(en)
A group of officers based in a labyrinthine top-secret prison must fight for their lives against Hatchet, a brilliant and infamous high-value detainee. When he escapes, his mysterious and deadly agenda has far reaching and dire consequences.
 6.2
6.2Shade(en)
Tiffany, Charlie and Vernon are con artists looking to up the ante from their typical scams. They figure a good way of doing this is taking down Dean "The Dean" Stevens, a well-known cardsharp, in a rigged game. However, they first need enough money to enter a game with Stevens, so they decide to strike a deal with fellow crook Larry Jennings to scam a local gangster -- which turns out to be a bad idea.
 6.0
6.0The 355(en)
A group of top female agents from American, British, Chinese, Colombian, and German government agencies are drawn together to try and stop an organization from acquiring a deadly weapon to send the world into chaos.
 5.9
5.9Until Death(en)
Anthony Stowe is a dirty cop who is hooked on heroin—and everyone hates him. After a serious accident, he is placed into an induced coma, but emerges from it a better person who wants to put things right.
 6.4
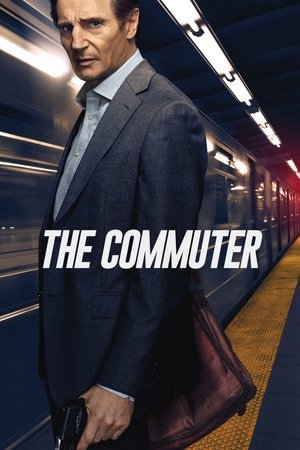
6.4The Commuter(en)
A businessman, on his daily commute home, gets unwittingly caught up in a criminal conspiracy that threatens not only his life but the lives of those around him.
 6.3
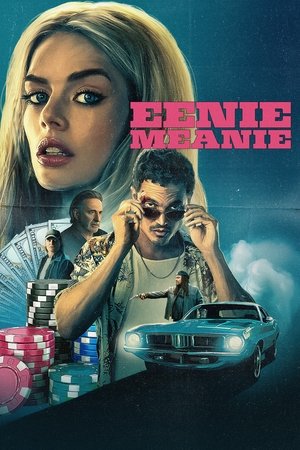
6.3Eenie Meanie(en)
A former teenage getaway driver gets dragged back into her unsavory past when a former employer offers her a chance to save the life of her chronically unreliable ex-boyfriend.
Similar Movies
 4.1
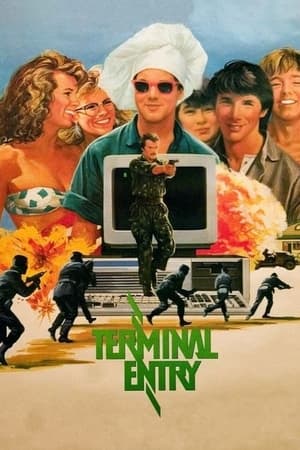
4.1Terminal Entry(en)
The USA is attacked by a large group of well organized terrorists who communicate through a computer network via satellite. A bunch of highschool kids has hacked the password and gained access. Believing it's a game they unknowingly cause terror acts all over the country. An anti-terror force fights against the terrorists.
 4.3
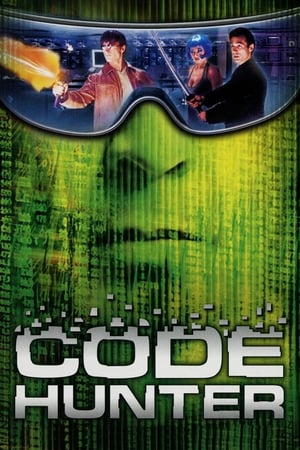
4.3Storm Watch(en)
America's best player is being pulled in to the ultimate cyber-terror. The game's mastermind has stolen his identity, put him on the FBI's Most Wanted List, and is blackmailing him to take a part in a real twisted plan of world destruction. With just hours left, can the code be broken to save the world from total annihilation?
 6.8
6.8Irumbu Thirai(ta)
Kathiravan, a major in the Indian army with anger management issues, is compelled by circumstances to borrow a loan from a bank with false documents. When the entire money in the account vanishes, Kathiravan tries to track down the scamsters, and it leads him to White Devil, a master hacker.
 0.0
0.0Guardians of the New World(en)
Guardians of the New World introduces us to the world of hacker culture. Emerging from the 70’s counterculture around conceptions of personal freedom, decentralisation of power and sharing, hacking really came to prominence with the emergence of the Internet as a ubiquitous public forum from the late 90’s onwards.
 7.4
7.4The Girl with the Dragon Tattoo(en)
Disgraced journalist Mikael Blomkvist investigates the disappearance of a weary patriarch's niece from 40 years ago. He is aided by the pierced, tattooed, punk computer hacker named Lisbeth Salander. As they work together in the investigation, Blomkvist and Salander uncover immense corruption beyond anything they have ever imagined.
 5.6
5.6Listening(en)
For years, we have tried to harness the power of the human mind… and failed. Now, one breakthrough will change everything. Beyond technology. Beyond humanity. Beyond control. David, Ryan, and Jordan hope the telepathy invention will solve all their problems, but the bleeding-edge technology opens a Pandora’s box of new dangers, as the team discovers that when they open their minds, there is nowhere to hide their thoughts.
 6.2
6.2I Am Kathalan(ml)
How many servers would you hack for love? What started as a silly attempt to win back his girlfriend turns into a dangerous game of revenge for Vishnu, risking everything he cherishes.
 6.0
6.0El App(es)
The life of one of the world's most renowned hackers is in danger after he develops an app that can hack any social media account and get any information using just a phone number.
 7.0
7.0Der Blinde(de)
An encounter with a blind man ends unexpectedly for Susan Howard. The supposedly helpless man stuns and kidnaps her. The case is handed over by the Home Secretary to Sir John, the head of Scotland Yard. He entrusts Chief Inspector Higgins and Superintendent Lane with the investigation. Their investigations quickly lead Higgins and Lane on the trail of murder, white slavery and blackmail.
 7.5
7.5Upgrade(en)
A brutal mugging leaves Grey Trace paralyzed in the hospital and his beloved wife dead. A billionaire inventor soon offers Trace a cure — an artificial intelligence implant called STEM that will enhance his body. Now able to walk, Grey finds that he also has superhuman strength and agility — skills he uses to seek revenge against the thugs who destroyed his life.
 6.4
6.4Cyberbully(en)
A chilling real-time thriller featuring a teenager, Casey, battling with an anonymous cyber-stalker.
 5.4
5.4The Throwaways(en)
Notorious hacker Drew Reynolds is captured by the CIA and given a proposition - work for them or spend the rest of his life in prison. Agreeing on the condition that he can form his own team, he puts together a group of "throwaways" - the people deemed expendable and seemingly the worst in the organization.
 5.2
5.2Ratter(en)
Emma is a young and beautiful graduate student just starting a new life in New York City. Like most people her age, she is always connected - her phone and laptop are constant companions, documenting her most intimate moments. What she doesn't realize is that she's sharing her life with an uninvited and dangerous guest. A hacker is following Emma’s every move. When the voyeuristic thrill of watching her digitally isn't enough, the situation escalates to a dangerous and terrifying level.
 4.8
4.8Hacker's Game(en)
A love story between two hackers, Soyan and Loise. Like many other hackers, Soyan works for a company he previously hacked.
 6.1
6.1Ghost in the Shell(en)
In the near future, Major is the first of her kind: a human saved from a terrible crash, then cyber-enhanced to be a perfect soldier devoted to stopping the world's most dangerous criminals.
 7.0
7.0Computer assault(es)
Each of the members of a group of hackers is willing to fight against system. Their messages and attacks are political, socially demmanding but also playful. Each of them have reasons to have moved to that virtual side, where they can be who they can't in real life. However, the sudden implication of authorities (pressed by goverment to be tougher against hackers)and of a wise and dangerous cracker will cause a turn in their crusade. Will they use the enemy's means or their ideological motivations imply a respect for law and human life?
 5.0
5.0Guayabo(es)
Two friends compete for a mysterious woman at a party. Next morning, she's found dead in the apartment of one of them, and they can't remember what happened.
 5.9
5.9The Steal(en)
A young American computer hackeress is hired by a liberal British lawyer to right the wrong done to a third world country by a London investment company. Even the expertise of her building inspector sidekick can not prevent a surprising development though.
 0.0
0.0Brooklyn Tide(en)
Two FBI agents pursue members of a radical hacker collective after they steal a powerful cyber-weapon.
 5.3
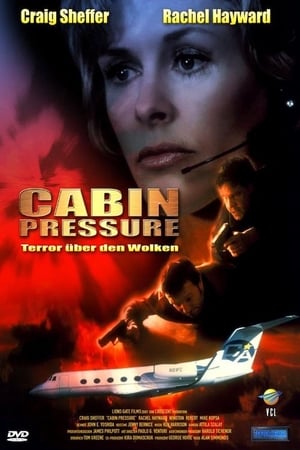
5.3Cabin Pressure(en)
A fully automated commercial jetliner is prepared to make its maiden voyage. Without an on-flight pilot, the craft relies on satellite linking for its course. But when the plane suddenly deviates from its determined route and establishes a circular pattern over Seattle, it becomes evident that the craft has been hijacked by a disgruntled former airline employee who has hacked into the flight's computer system from his apartment, somewhere in the United States. Now, a former discredited Navy pilot and an oddball technician must race against the clock to find where the angry employee is, and regain control of the plane before it crashes into the city.