Intoxicant
Top 4 Billed Cast

匿名遊戲
HomePage
Overview
A hacker named Intoxicant is threatening to destroy a famous internet forum. While people are gathering in the system and expecting something to happen, six different users begins to suspect each other. When the countdown of annihilation begins, the chaos between trust and truth is about to grow.
Release Date
2008-06-16
Average
8
Rating:
4.0 startsTagline
Genres
Languages:
普通话Keywords
Similar Movies
 7.8
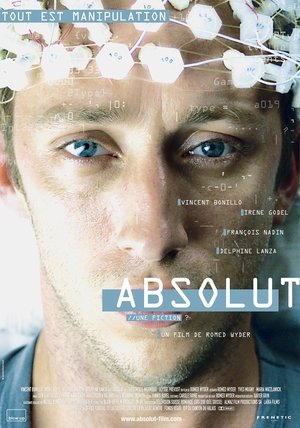
7.8Absolut(en)
Two guys against globalization want to plant a virus in the network of a finance corporation. On the day of the attack Alex has an accident and cannot remember anything. Visions and reality are thrown together in a confusing maze. Alex tries to escape from this muddle but what he discovers turns out to be rather frightening…
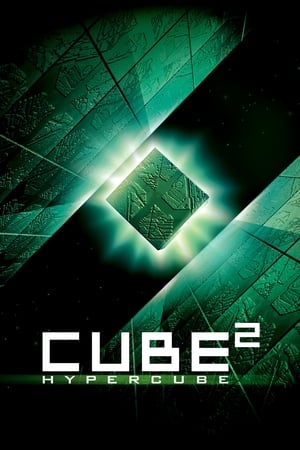 5.5
5.5Cube 2: Hypercube(en)
Eight strangers awaken with no memory, in a puzzling cube-shaped room where the laws of physics do not always apply.
 7.1
7.1WarGames(en)
High school student David Lightman has a talent for hacking. But while trying to hack into a computer system to play unreleased video games, he unwittingly taps into the Department of Defense's war computer and initiates a confrontation of global proportions. Together with his friend and a wizardly computer genius, David must race against time to outwit his opponent and prevent a nuclear Armageddon.
 6.0
6.0The Net(en)
Angela Bennett is a freelance computer systems analyst who tracks down software viruses. At night she hooks up to the internet and chats to others 'surfing the net'. While de-bugging a new high-tech game for a cyber friend, she comes across a top secret program and becomes the target of a mysterious organization who will stop at nothing to erase her identity and her existence, in order to protect the project.
 6.6
6.6Live Free or Die Hard(en)
John McClane is back and badder than ever, and this time he calls on the services of a young hacker in his bid to stop a ring of Internet terrorists intent on taking control of America's computer infrastructure.
 6.8
6.823(de)
The movie's plot is based on the true story of a group of young computer hackers from Hannover, Germany. In the late 1980s the orphaned Karl Koch invests his heritage in a flat and a home computer. At first he dials up to bulletin boards to discuss conspiracy theories inspired by his favorite novel, R.A. Wilson's "Illuminatus", but soon he and his friend David start breaking into government and military computers. Pepe, one of Karl's rather criminal acquaintances senses that there is money in computer cracking - he travels to east Berlin and tries to contact the KGB.
 4.7
4.7Double Down(en)
An edgy action thriller set in Las Vegas during a terrorist attack. A genius computer loner takes control of the city and the attack as he fights with his fits of overwhelming depression and obsessions with love and death.
 6.5
6.5Nirvana(it)
Jimi, a computer game designer, finds that his latest product has been infected by a virus which has given consciousness to the main character of the game, Solo. Tormented by the memory of his fled girlfriend Lisa and begged by Solo to end its useless "life", Jimi begins a search for people who can help him both to discover what happened to Lisa and to delete his game before it is released.
 6.6
6.6Night Hunter(en)
A Minnesota police officer crosses paths with a committed and tireless vigilante as he follows the trail of a ruthless predator responsible for several abductions and murders.
 6.9
6.9So Close(cn)
A conflict of interest between two high-kicking assassin sisters is complicated as they're pursued by the criminals who hired them and an equally high-kicking female cop.
 6.2
6.2Assassination Nation(en)
After an anonymous hacker begins leaking the private data of thousands living in a small American town, the townspeople spiral into madness, with four high school seniors at the center of the maelstrom.
 6.2
6.2The Girl in the Spider's Web(en)
After being enlisted to recover a dangerous computer program, hacker Lisbeth Salander and journalist Mikael Blomkvist find themselves caught in a web of spies, cybercriminals and corrupt government officials.
 7.7
7.7Fabricated City(ko)
In real life, Kwon Yoo is unemployed, but in the virtual game world he is the best leader. Kwon Yoo is then framed for a murder. With the help of hacker Yeo-wool, he tries to uncover the truth behind the murder case.
 6.3
6.3Swordfish(en)
Rogue agent Gabriel Shear is determined to get his mitts on $9 billion stashed in a secret Drug Enforcement Administration account. He wants the cash to fight terrorism, but lacks the computer skills necessary to hack into the government mainframe. Enter Stanley Jobson, a n'er-do-well encryption expert who can log into anything.
 5.8
5.8Firewall(en)
State-of-the-art security system creator Jack Stanfield has cemented his reputation as a man who's thought of everything. But when a criminal finds a way into his personal life, everything Jack holds dear is suddenly at stake.
 5.1
5.1The Net 2.0(en)
The life of a young computer systems analyst is thrown into turmoil after arriving in Istanbul to start a new job. She soon finds her passport missing, her credit cards useless, her bank account empty and her identity stolen. As the story progresses we find people and events may not be what they seem.
 5.2
5.2Escape Plan 2: Hades(en)
Ray Breslin manages an elite team of security specialists trained in the art of breaking people out of the world's most impenetrable prisons. When his most trusted operative, Shu Ren, is kidnapped and disappears inside the most elaborate prison ever built, Ray must track him down with the help of some of his former friends.
 4.3
4.3Dot.Kill(en)
Charlie Daines is a morphine-addicted detective on the trail of a psychopath who is setting up murders and broadcasting them live on the internet. As he closes in on the killer, Charlie realises that he is to be the final victim.
 6.4
6.4Hackers(en)
Along with his new friends, a teenager who was arrested by the US Secret Service and banned from using a computer for writing a computer virus discovers a plot by a nefarious hacker, but they must use their computer skills to find the evidence while being pursued by the Secret Service and the evil computer genius behind the virus.
Recommendations Movies
 6.1
6.1Takedown(en)
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...
 7.3
7.3Zero Days(en)
Alex Gibney explores the phenomenon of Stuxnet, a self-replicating computer virus discovered in 2010 by international IT experts. Evidently commissioned by the US and Israeli governments, this malware was designed to specifically sabotage Iran’s nuclear programme. However, the complex computer worm ended up not only infecting its intended target but also spreading uncontrollably.
 6.2
6.2Assassination Nation(en)
After an anonymous hacker begins leaking the private data of thousands living in a small American town, the townspeople spiral into madness, with four high school seniors at the center of the maelstrom.
 6.2
6.2The Most Hated Woman in America(en)
The true story of Madalyn Murray O'Hair -- iconoclast, opportunist, and outspoken atheist -- from her controversial rise to her untimely demise.
 6.6
6.62073(en)
Inspired by Chris Marker's iconic 1962 featurette La Jetée; the year is 2073—a not-so-distant dystopian future—and the setting is New San Francisco, the scorched-earth tech-dominant police state where democracy and personal freedom have been well and truly obliterated.
 6.1
6.1Chief of Station(en)
After learning that the death of his wife was not an accident, a former CIA Station Chief is forced back into the espionage underworld, teaming up with an adversary to unravel a conspiracy that challenges everything he thought he knew.
 6.0
6.0Interceptor(en)
A U.S. Army Captain uses her years of tactical training to save humanity from sixteen nuclear missiles launched at the U.S. as a violent attack threatens her remote missile interceptor station.
 6.0
6.0Point Blank(en)
A nurse is forced to spring a wounded murder suspect from the hospital when the man’s brother kidnaps his pregnant wife and wants to make a trade.
 6.2
6.2Occupation: Rainfall(en)
Two years into an intergalactic invasion of Earth, survivors in Sydney, Australia, fight back in a desperate ground war. As casualties mount by the day, the resistance and their unexpected allies, uncover a plot that could see the war come to a decisive end. With the Alien invaders hell-bent on making earth their new home, the race is on to save mankind.
 5.9
5.9Dark Web: Cicada 3301(en)
Genius hacker Connor discovers Cicada 3301, an online treasure hunt that could be a recruiting tool for a secret society. Soon Conner, art-expert friend Avi, and secretive librarian Gwen are dashing from graffiti sites to ancient libraries to uncover real-world clues. But they must outrun aggressive NSA agents, also hot on the trail of Cicada, who want the glory for themselves.
 6.1
6.1The MacKintosh Man(en)
A member of British Intelligence assumes a fictitious criminal identity and allows himself to be caught, imprisoned, and freed in order to infiltrate a spy organization and expose a traitor; only, someone finds him out and exposes him to the gang...
 6.3
6.3Code 8 Part II(en)
In a world where superpowered people are heavily policed by robots, an ex-con teams up with a drug lord he despises to protect a teen from a corrupt cop.
 5.9
5.9Hellion(en)
When motocross and heavy metal obsessed, 13-year-old Jacob's delinquent behavior forces CPS to place his little brother Wes with his aunt, Jacob and his emotionally absent father must finally take responsibility for their actions and each other in order to bring Wes home.
 6.0
6.0The Fifth Estate(en)
A look at the relationship between WikiLeaks founder Julian Assange and his early supporter and eventual colleague Daniel Domscheit-Berg, and how the website's growth and influence led to an irreparable rift between the two friends.
 6.0
6.0Hypnotic(en)
A young woman seeking self-improvement enlists the help of a renowned hypnotist but, after a handful of intense sessions, discovers unexpected and deadly consequences.
 6.2
6.2The Marine 3: Homefront(en)
A Marine must do whatever it takes to save his kidnapped sister and stop a terrorist attack masterminded by a radical militia group.
 5.9
5.9uwantme2killhim?(en)
Based on the Vanity Fair article of the same title, a story about a young boy drawn into a web of lies through an online chatroom.
 6.2
6.2The Invention of Lying(en)
Set in a world where the concept of lying doesn't exist, a loser changes his lot when he invents lying and uses it to get ahead.
 6.0
6.0Dangerous Game: The Legacy Murders(en)
A family reunion at a remote mansion takes a lethal turn when they are trapped inside and forced to play a deadly survival game where only one will make it out alive.
 5.8
5.8The Girl in the Book(en)
The story of a young writer's transformation when her past invades her present.