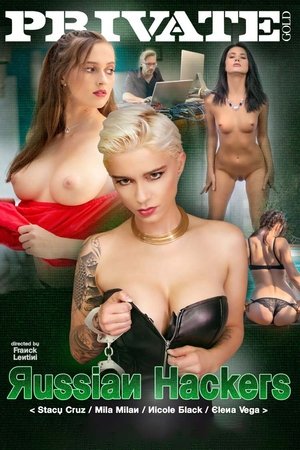
Russian Hackers[2019]
Can one man topple an entire government? Can one man alone jeopardise the safety of millions? In Private Gold, Russian Hackers it sure seems that way, the police are concerned and that’s why they’ve put together a super team of girls ready to the exploit the one weakness of their most wanted criminal hacker, Alexei. Watch team leader Mila Milan lead the talented and extremely sexy taskforce of Nicole Black, Elana Vega and Stacy Cruz on a chase to do what’s ever necessary to catch him. Alexei is smart, but he’s a man all the same and there’s no way he will be able to resist these girls. So strap in and get ready for an exhilarating man hunt, with four new girls and a whole lot of sex in Private Gold, Russian Hackers.

Movie: Russian Hackers
Recommendations Movies
 7.3
7.3Zero Days(en)
Alex Gibney explores the phenomenon of Stuxnet, a self-replicating computer virus discovered in 2010 by international IT experts. Evidently commissioned by the US and Israeli governments, this malware was designed to specifically sabotage Iran’s nuclear programme. However, the complex computer worm ended up not only infecting its intended target but also spreading uncontrollably.
 6.2
6.2Assassination Nation(en)
After an anonymous hacker begins leaking the private data of thousands living in a small American town, the townspeople spiral into madness, with four high school seniors at the center of the maelstrom.
 6.1
6.1...All the Marbles(en)
A two-bit promoter tries to take a women's wrestling team to the top.
 5.8
5.8Pretty Persuasion(en)
A 15-year-old girl incites chaos among her friends and a media frenzy when she accuses her drama teacher of sexual harassment.
 6.6
6.6Trafficked(en)
In this story inspired by real characters, three girls from America, Nigeria and India are trafficked through an elaborate global network and enslaved in a Texas brothel, and must together attempt a daring escape to reclaim their freedom.
 5.9
5.9GirlHouse(en)
In an attempt to make some extra cash while away at College, Kylie moves into a house that streams content to an X-rated website. After a deranged fan hacks in to determine the house's location, she finds herself in a terrifying fight for her life.
 6.6
6.6Fear(en)
Nicole Walker always dreamed of being swept away by someone special — someone strong, sexy and sensitive who would care for her more than anything else in the world. David is all that and more: a modern-day knight who charms and seduces her, body and soul. But her perfect boyfriend is not all he seems to be. His sweet facade masks a savage, dark side that will soon transform Nicole's dream into a nightmare.
 6.0
6.0Sniper: Legacy(en)
A rogue gunman is assassinating high-ranking military officers one by one. When Gunnery Sgt. Brandon Beckett is informed his father, legendary shooter Thomas Beckett has been killed, Brandon springs into action to take out the perpetrator.
 5.9
5.968 Kill(en)
Chip's problem is that he can't say no to beautiful women. This weakness gets him into a world of trouble when he agrees to help his girlfriend steal $68,000.
 6.2
6.2Death Wish 3(en)
Architect/vigilante Paul Kersey arrives back in New York City and is forcibly recruited by a crooked police chief to fight street crime caused by a large gang terrorizing the neighborhoods.
 6.1
6.1The Den(en)
A young woman studying the habits of webcam chat users from the apparent safety of her apartment witnesses a brutal murder online and is quickly immersed in a nightmare in which she and her loved ones are targeted for the same grisly fate as the first victim.
 7.9
7.9Nobody(en)
Hutch Mansell, a suburban dad, overlooked husband, nothing neighbor — a "nobody." When two thieves break into his home one night, Hutch's unknown long-simmering rage is ignited and propels him on a brutal path that will uncover dark secrets he fought to leave behind.
 6.4
6.4Just Before I Go(en)
Ted Morgan has been treading water for most of his life. After his wife leaves him, Ted realizes he has nothing left to live for. Summoning the courage for one last act, Ted decides to go home and face the people he feels are responsible for creating the shell of a person he has become. But life is tricky. The more determined Ted is to confront his demons, to get closure, and to withdraw from his family, the more Ted is yanked into the chaos of their lives. So, when Ted Morgan decides to kill himself, he finds a reason to live.
 7.2
7.2Kiss Me Deadly(en)
One evening, Hammer gives a ride to Christina, an attractive hitchhiker on a lonely country road, who has escaped from the nearby lunatic asylum. Thugs waylay them and force his car to crash. When Hammer returns to semi-consciousness, he hears Christina being tortured until she dies. Hammer, both for vengeance and in hopes that "something big" is behind it all, decides to pursue the case.
 6.3
6.3The Substitute 2: School's Out(en)
When teacher Randall Thomasson is killed during a carjacking, an unexpected visitor shows up at his funeral - his estranged brother, Karl Thomasson. An ex-Green Beret turned mercenary, Karl signs on as a new substitute teacher in order to investigate Randall's murder.
 6.0
6.0Lockdown(en)
Avery (Jones) returns to college as a competitive swimmer after getting his life back on track. But his life takes another unexpected turn when he and his two friends (Bonds, Casseus) are wrongly accused of murder and end up in prison.
 6.1
6.1Original Sin(en)
A young man is plunged into a life of subterfuge, deceit and mistaken identity in pursuit of a femme fatale whose heart is never quite within his grasp.
 6.1
6.1Orgazmo(en)
A devout Mormon living in L.A. becomes a pornographic actor after his martial arts moves impress a big-time director.
 6.5
6.5Jarhead: Law of Return(en)
Major Ronan Jackson, an accomplished fighter pilot for the Israel Defense Forces and son of a U.S. Senator, is shot down while flying through Syrian airspace. After miraculously surviving the crash, Jackson is taken captive by a group of Hezbollah militiamen. A squad of elite soldiers, led by Gunnery Sergeant Dave Torres, risk their own lives in the hopes of saving an ally they've never met.
Similar Movies
 5.5
5.5Cube 2: Hypercube(en)
Eight strangers awaken with no memory, in a puzzling cube-shaped room where the laws of physics do not always apply.
 8.2
8.2The Matrix(en)
Set in the 22nd century, The Matrix tells the story of a computer hacker who joins a group of underground insurgents fighting the vast and powerful computers who now rule the earth.
 7.8
7.8Absolut(en)
Two guys against globalization want to plant a virus in the network of a finance corporation. On the day of the attack Alex has an accident and cannot remember anything. Visions and reality are thrown together in a confusing maze. Alex tries to escape from this muddle but what he discovers turns out to be rather frightening…
 6.6
6.6Tron(en)
When brilliant video game maker Flynn hacks the mainframe of his ex-employer, he is beamed inside an astonishing digital world and becomes part of the very game he is designing. In his mission through cyberspace, Flynn matches wits with a maniacal Master Control Program and teams up with Tron, a security measure created to bring balance to the digital environment.
 6.9
6.9Sneakers(en)
When shadowy U.S. intelligence agents blackmail a reformed computer hacker and his eccentric team of security experts into stealing a code-breaking 'black box' from a Soviet-funded genius, they uncover a bigger conspiracy. Now, he and his 'sneakers' must save themselves and the world economy by retrieving the box from their blackmailers.
 7.1
7.1WarGames(en)
High school student David Lightman has a talent for hacking. But while trying to hack into a computer system to play unreleased video games, he unwittingly taps into the Department of Defense's war computer and initiates a confrontation of global proportions. Together with his friend and a wizardly computer genius, David must race against time to outwit his opponent and prevent a nuclear Armageddon.
 6.8
6.823(de)
The movie's plot is based on the true story of a group of young computer hackers from Hannover, Germany. In the late 1980s the orphaned Karl Koch invests his heritage in a flat and a home computer. At first he dials up to bulletin boards to discuss conspiracy theories inspired by his favorite novel, R.A. Wilson's "Illuminatus", but soon he and his friend David start breaking into government and military computers. Pepe, one of Karl's rather criminal acquaintances senses that there is money in computer cracking - he travels to east Berlin and tries to contact the KGB.
 6.8
6.8eXistenZ(en)
A game designer on the run from assassins must play her latest virtual reality creation with a marketing trainee to determine if the game has been damaged.
 6.6
6.6Nicotina(es)
A hacker who is spying on a pretty neighbour messes up his assignment to break into Swiss bank accounts for Russian mobsters.
 0.0
0.0Russia's Cyber Army(ru)
For years now, the Kremlin has been systematically trying to use well-trained hackers for its own benefit. In exchange for freedom and protection, they do the dirty work of the state, interfering in other countries’ elections and penetrating government networks. Just how dangerous is Russia’s cyber army?
 5.5
5.5Offline: Are You Ready for the Next Level?(de)
Champion gamer Jan has to fight for his digital identity, winning back his real life as well.
 5.4
5.4Sync(en)
Every 15 seconds, a computer, network, or mobile device is hacked by cyber-terrorists. To combat this problem, Syntek Industries has manufactured data couriers designed from advanced machine robotics. These couriers are known as SYNCS. Syncs are programmed to securely deliver data packages without interruption.
 0.0
0.0Once Upon A Heist(en)
A man named Charlie Nelson is recruited by an anonymous user who goes by the codename "echo" to put together the perfect heist in which Charlie, his brother Nick, and two associates, James Freeman and Mike Allen would attempt to steal ten million dollars worth of gold.
 5.6
5.6Fled(en)
During a routine prison work detail, convict Piper is chained to Dodge, a cyberhacker, when gunfire breaks out. Apparently, the attack is related to stolen money that the Mafia is after, and some computer files that somebody wants desperately to bury. The pair, who don't exactly enjoy each other's company, escape and must work together if they are to reach Atlanta alive. Luckily, they meet a woman who may be willing to help them.
 7.5
7.5Ghost in the Shell: Stand Alone Complex - Solid State Society(ja)
The story takes place in the year 2034, two years after the events in Ghost in the Shell: S.A.C. 2nd GIG. Female cyborg Major Motoko Kusanagi has left Public Security Section 9, an elite counter-terrorist and anti-crime unit specializing in cyber-warfare, which has expanded to a team of 20 field operatives with Togusa acting as the field lead.
 5.1
5.1The District(hu)
In an effort to end family feuding, a young gypsy travels back in time to kill mammoths to ensure Hungary becomes rich by killing mammoths in order to create a massive oil reservoir. Things don't go entirely according to plan...
 5.1
5.1Fair Game(en)
Max Kirkpatrick is a cop who protects Kate McQuean, a civil law attorney, from a renegade KGB team out to terminate her
 6.1
6.1Hackers Are People Too(en)
A portrait of the hacking community. In an effort to challenge preconceived notions and media-driven stereotypes Hackers Are People Too lets hackers speak for themselves and introduce their community to the public.
 6.4
6.4In the Realm of the Hackers(en)
In The Realm of the Hackers is a documentary about the prominent hacker community, centered in Melbourne, Australia in the late 80's to early 1990. The storyline is centered around the Australian teenagers going by the hacker names "Electron" and "Phoenix", who were members of an elite computer hacking group called The Realm and hacked into some of the most secure computer networks in the world, including those of the US Naval Research Laboratory, Lawrence Livermore National Laboratory, a government lab charged with the security of the US nuclear stockpile, and NASA.