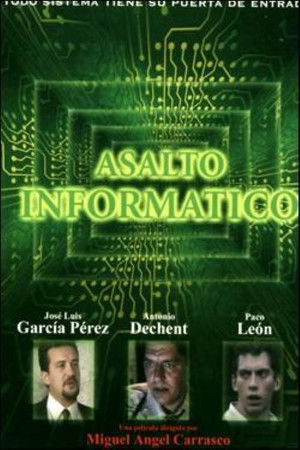
Computer assault(2002)
Each of the members of a group of hackers is willing to fight against system. Their messages and attacks are political, socially demmanding but also playful. Each of them have reasons to have moved to that virtual side, where they can be who they can't in real life. However, the sudden implication of authorities (pressed by goverment to be tougher against hackers)and of a wise and dangerous cracker will cause a turn in their crusade. Will they use the enemy's means or their ideological motivations imply a respect for law and human life?





Movie: Computer assault
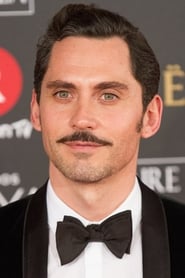
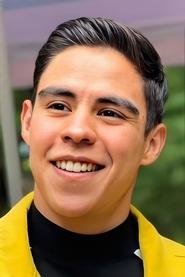
Top 10 Billed Cast
Paloma
Joven Hacker
Agente 2
Policia
Asalto informático
HomePage
Overview
Each of the members of a group of hackers is willing to fight against system. Their messages and attacks are political, socially demmanding but also playful. Each of them have reasons to have moved to that virtual side, where they can be who they can't in real life. However, the sudden implication of authorities (pressed by goverment to be tougher against hackers)and of a wise and dangerous cracker will cause a turn in their crusade. Will they use the enemy's means or their ideological motivations imply a respect for law and human life?
Release Date
2002-01-04
Average
7
Rating:
3.5 startsTagline
Genres
Languages:
EspañolKeywords
Recommendations Movies
 6.1
6.1Takedown(en)
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...
 6.2
6.2Infidelity in Suburbia(en)
With her husband away at work, and her son at school, Laura dreams of a home-renovation project to supplant her restless days. Elliott, her irresistibly hot private contractor, soon fulfills her more forbidden dreams.
 6.4
6.4Cyberbully(en)
A chilling real-time thriller featuring a teenager, Casey, battling with an anonymous cyber-stalker.
 6.4
6.4Secrets at the Lake(en)
A group of teens make a pact that has deadly consequences.
 7.3
7.3Zero Days(en)
Alex Gibney explores the phenomenon of Stuxnet, a self-replicating computer virus discovered in 2010 by international IT experts. Evidently commissioned by the US and Israeli governments, this malware was designed to specifically sabotage Iran’s nuclear programme. However, the complex computer worm ended up not only infecting its intended target but also spreading uncontrollably.
 7.1
7.1We Are Legion: The Story of the Hacktivists(en)
Takes us inside the world of Anonymous, the radical "hacktivist" collective that has redefined civil disobedience for the digital age. The film explores early hacktivist groups like Cult of the Dead Cow and Electronic Disturbance Theater, then moves to Anonymous' raucous beginnings on the website 4chan. Through interviews with current members, people recently returned from prison or facing trial, writers, academics, activists and major players in various "raids," the documentary traces Anonymous’ evolution from merry pranksters to a full-blown movement with a global reach, the most transformative civil disobedience of our time.
 5.9
5.9The Man from Rome(es)
A computer hacker penetrates Vatican security and sends an urgent anonymous plea to the pope. Handsome Father Quart, of the church's Institute of External Affairs, an arm of the Vatican intelligence, is dispatched to investigate. The message of the hacker concerns a crumbling 17th century Baroque church in the heart of Seville that apparently "kills to defend itself".
 6.9
6.9Sneakers(en)
When shadowy U.S. intelligence agents blackmail a reformed computer hacker and his eccentric team of security experts into stealing a code-breaking 'black box' from a Soviet-funded genius, they uncover a bigger conspiracy. Now, he and his 'sneakers' must save themselves and the world economy by retrieving the box from their blackmailers.
 6.0
6.0The Signal(en)
On a road trip, Nic and two friends are drawn to an isolated area by a computer genius. When everything suddenly goes dark, Nic regains consciousness – only to find himself in a waking nightmare.
 6.6
6.6Nicotina(es)
A hacker who is spying on a pretty neighbour messes up his assignment to break into Swiss bank accounts for Russian mobsters.
 5.9
5.9Dark Web: Cicada 3301(en)
Genius hacker Connor discovers Cicada 3301, an online treasure hunt that could be a recruiting tool for a secret society. Soon Conner, art-expert friend Avi, and secretive librarian Gwen are dashing from graffiti sites to ancient libraries to uncover real-world clues. But they must outrun aggressive NSA agents, also hot on the trail of Cicada, who want the glory for themselves.
 6.6
6.6Hostage House(en)
A realtor and her daughter are taken hostage by armed robbers.
 6.1
6.1Chief of Station(en)
After learning that the death of his wife was not an accident, a former CIA Station Chief is forced back into the espionage underworld, teaming up with an adversary to unravel a conspiracy that challenges everything he thought he knew.
 6.5
6.5Kept Woman(en)
Jessica and her fiancé Evan just moved from the city into their dream home on a quiet suburban street. Soon after, Jessica catches her seemingly friendly new neighbor, Simon, in a strange lie and can't let her suspicions rest. The danger escalates when Simon lures her inside his home and imprisons Jessica in his secret bunker, meticulously decorated in the idealized style of the 1950's.
 6.5
6.5Downloaded(en)
A documentary that explores the downloading revolution; the kids that created it, the bands and the businesses that were affected by it, and its impact on the world at large.
 6.9
6.9Lights Out(en)
A drifting ex-soldier turns underground fighter with the help of a just-released ex-con, pitting him against corrupt cops and hired killers now gunning for him and all those he cares about.
 5.9
5.9Twisted(en)
Kara and Tyler are close to marriage when Tyler’s dangerous ex-girlfriend returns from rehab, and is adamant on winning him back, pulling Kara into a twisted game of cat and mouse.
 6.0
6.0Stalked by My Doctor(en)
When a teenage girl is miraculously saved by a heart surgeon, the doctor begins to flirt with her. Her father doesn’t believe her and unbeknownst to all, the doctor is obsessed with the girl.
 6.4
6.4Seeds of Yesterday(en)
The Sheffield family reveal and go through some home truths as their middle child inherits the Foxworth mansion. The family's ghosts looming over, and more tragedies are in store as the curse lives on.
 5.9
5.9Sayen: The Huntress(es)
Realizing that she cannot take down Fisk alone, Sayen teams up with an underground resistance group with a plan to expose and end Fisk's unchecked plundering once and for all.
Similar Movies
 6.8
6.823(de)
The movie's plot is based on the true story of a group of young computer hackers from Hannover, Germany. In the late 1980s the orphaned Karl Koch invests his heritage in a flat and a home computer. At first he dials up to bulletin boards to discuss conspiracy theories inspired by his favorite novel, R.A. Wilson's "Illuminatus", but soon he and his friend David start breaking into government and military computers. Pepe, one of Karl's rather criminal acquaintances senses that there is money in computer cracking - he travels to east Berlin and tries to contact the KGB.
 7.3
7.3The Devil's Backbone(es)
Spain, 1939. In the last days of the Spanish Civil War, the young Carlos arrives at the Santa Lucía orphanage, where he will make friends and enemies as he follows the quiet footsteps of a mysterious presence eager for revenge.
 6.4
6.4Vantage Point(en)
During an historic counter-terrorism summit in Spain, the President of the United States is struck down by an assassin's bullet. Eight strangers have a perfect view of the kill, but what did they really see? As the minutes leading up to the fatal shot are replayed through the eyes of each eyewitness, the reality of the assassination takes shape.
 6.5
6.5Nirvana(it)
Jimi, a computer game designer, finds that his latest product has been infected by a virus which has given consciousness to the main character of the game, Solo. Tormented by the memory of his fled girlfriend Lisa and begged by Solo to end its useless "life", Jimi begins a search for people who can help him both to discover what happened to Lisa and to delete his game before it is released.
 7.1
7.1The Girl Who Kicked the Hornet's Nest(sv)
After taking a bullet to the head, Salander is under close supervision in a hospital and is set to face trial for attempted murder on her eventual release. With the help of journalist Mikael Blomkvist and his researchers at Millennium magazine, Salander must prove her innocence. In doing this she plays against powerful enemies and her own past.
 6.8
6.8Naked Weapon(cn)
A mysterious woman, known as Madame M, kidnaps forty pre-teen girls and transports them to a remote island to train them as the most deadly assassins. CIA operative Jack Chen follows the case for 6 years with no leads, but when a series of assassinations begin to occur, Jack suspects that Madame M is back in business.
 5.6
5.6The Marriage of Figaro(fr)
Comedy in five acts by Beaumarchais, filmed by Marcel Bluwal in studio and on location. The cast, in accordance with Marcel Bluwal's wishes, is in keeping with the age and character of the characters, to give it rhythm. At once "a comic baroque play, a bourgeois drama, a chansonnier's number, a social satire, a farce and a very pretty love story" according to Marcel Bluwal, it can also be summed up, according to Beaumarchais, as "the most bantering of intrigues".
 6.6
6.6Nicotina(es)
A hacker who is spying on a pretty neighbour messes up his assignment to break into Swiss bank accounts for Russian mobsters.
 3.3
3.3Lawnmower Man 2: Beyond Cyberspace(en)
Now a shattered mind lurking in cyberspace, Jobe plots a return by hijacking a global VR network and rebuilding himself as something far beyond human. As reality starts to glitch, a small group races to stop a digital god who no longer needs a body.
 6.4
6.4Hackers(en)
Along with his new friends, a teenager who was arrested by the US Secret Service and banned from using a computer for writing a computer virus discovers a plot by a nefarious hacker, but they must use their computer skills to find the evidence while being pursued by the Secret Service and the evil computer genius behind the virus.
 6.1
6.1Takedown(en)
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...
 4.8
4.8Stolen Identity 2(ja)
A couple of months have passed since the serial murder case. A new dead body is found in the same area. Detective Manabu Kagaya tries to find the truth. He goes to see serial killer Yoshiharu Urano in prison.
 6.9
6.9So Close(cn)
A conflict of interest between two high-kicking assassin sisters is complicated as they're pursued by the criminals who hired them and an equally high-kicking female cop.
 7.5
7.5The Girl with the Dragon Tattoo(sv)
Swedish thriller based on Stieg Larsson's novel about a male journalist and a young female hacker. In the opening of the movie, Mikael Blomkvist, a middle-aged publisher for the magazine Millennium, loses a libel case brought by corrupt Swedish industrialist Hans-Erik Wennerström. Nevertheless, he is hired by Henrik Vanger in order to solve a cold case, the disappearance of Vanger's niece
 5.5
5.5The Cache(nl)
Highly intelligent hacker Lillian joins a cybersecurity company in order to gain access to the bank where her father used to work. She discovers nothing is what it seems and it turns out she isn’t the only one pretending to be someone else. But where do we draw the line between activism and terrorism?
 6.5
6.5Nackt. Das Netz vergisst nie.(de)
16-year-old Lara takes nude photos for her boyfriend, which soon flood social media. Lara's phone has been hacked, the photos published, and she's being blackmailed.
 6.1
6.1Shiver(es)
Santi, a young high-school student with a serious physical reaction to sunlight, is forced by his health to move with his single mother to a shadowy, isolated village in the mountains of Spain where the inhabitants begin to reveal themselves as strangely xenophobic. When terrible, violent events begin to occur, Santi becomes first a pariah at school and then strongly suspected by the police of hideous murders. Santi himself, however, wonders if he is not the next victim.
 7.6
7.6Who Am I(de)
Benjamin, a young German computer whiz, is invited to join a subversive hacker group that wants to be noticed on the world's stage.
 6.3
6.3The Cheetah Girls 2(en)
Best friends Galleria, Chanel, Dorinda, and Aqua, A.K.A. the girl band "The Cheetahs," get the opportunity of a lifetime when they strut their way to Barcelona, Spain, to perform in an international music festival. Along the way, the "amigas Cheetahs" learn that, although their paths are not the same, they are lucky to have one another for the journey.
 5.5
5.5Cube 2: Hypercube(en)
Eight strangers awaken with no memory, in a puzzling cube-shaped room where the laws of physics do not always apply.