The Cicada Code(2024)
There is no peace without freedom.
In a Brazil taken over by a new dictatorial regime, Íris, a young hacker whose father was taken as a political prisoner, discovers an online challenge from a secret organization known only as 'Cicada,' which will set her on a journey that could change the course of the country... and also uncover what really happened to her father.
Movie: The Cicada Code
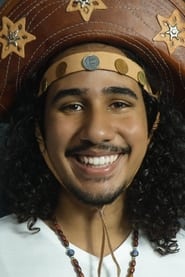
Top 10 Billed Cast
Íris
Tomás
Arya (voice)
Ministro de Defesa
Repórter 1
Repórter 2
Atendente

O Código Cicada
HomePage
Overview
In a Brazil taken over by a new dictatorial regime, Íris, a young hacker whose father was taken as a political prisoner, discovers an online challenge from a secret organization known only as 'Cicada,' which will set her on a journey that could change the course of the country... and also uncover what really happened to her father.
Release Date
2024-10-13
Average
0
Rating:
0.0 startsTagline
There is no peace without freedom.
Genres
Languages:
PortuguêsKeywords
Similar Movies
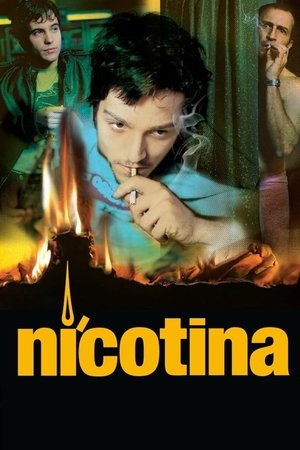 6.6
6.6Nicotina(es)
A hacker who is spying on a pretty neighbour messes up his assignment to break into Swiss bank accounts for Russian mobsters.
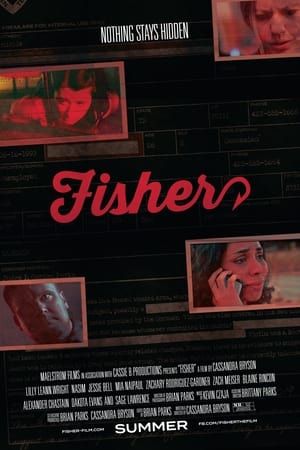 2.5
2.5Fisher(en)
In the small town of Eden, Tennessee, a neglected and naive teenage girl named Clara Banks has made a habit of deceiving people online for gifts, a gambit known as "catfishing." She thinks it's all fun and games until she hooks the attention of the wrong person. A short time later, events set into motion spiral out of control as someone begins stalking Clara and her friends. As the consequences of her actions return to haunt her, twisted messages start showing up at Clara's home, causing her to fear for her life. Will she ever feel safe again now that the evil has come knocking?
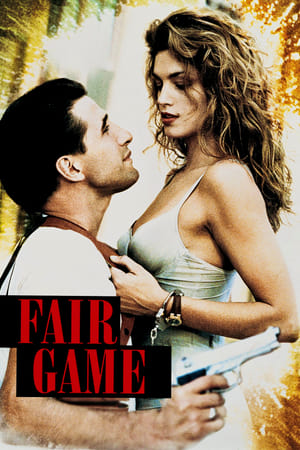 5.1
5.1Fair Game(en)
Max Kirkpatrick is a cop who protects Kate McQuean, a civil law attorney, from a renegade KGB team out to terminate her
 7.6
7.6Who Am I(de)
Benjamin, a young German computer whiz, is invited to join a subversive hacker group that wants to be noticed on the world's stage.
 3.3
3.3Lawnmower Man 2: Beyond Cyberspace(en)
After being rescued from the ruins of Virtual Space Industries, Jobe is rebuilt and reconnected to virtual reality by corporate mogul Jonathan Walker. Years later, teenage hacker Peter Parkette helps Jobe locate Benjamin Trace, the original creator of virtual reality, only to uncover Jobe’s plan to launch a new world order using Walker’s tech. Now, Peter, Trace, Cori, and a band of runaways must stop Jobe and Walker before they enslave humanity through cyberspace.
 5.8
5.8Firewall(en)
State-of-the-art security system creator Jack Stanfield has cemented his reputation as a man who's thought of everything. But when a criminal finds a way into his personal life, everything Jack holds dear is suddenly at stake.
 5.1
5.1The Net 2.0(en)
The life of a young computer systems analyst is thrown into turmoil after arriving in Istanbul to start a new job. She soon finds her passport missing, her credit cards useless, her bank account empty and her identity stolen. As the story progresses we find people and events may not be what they seem.
 6.0
6.0Antitrust(en)
A computer programmer's dream job at a hot Portland-based firm turns nightmarish when he discovers his boss has a secret and ruthless means of dispatching anti-trust problems.
 5.8
5.8Stay Alive(en)
After the brutal death of a friend, a group of friends find themselves in possession of a video-game called "Stay Alive," a blood-curdling true story of a 17th century noblewoman known as the Blood Countess. After playing the game when they know they shouldn't, however, the friends realize that once they die in the game — they die for real!
 6.5
6.5Nirvana(it)
Jimi, a computer game designer, finds that his latest product has been infected by a virus which has given consciousness to the main character of the game, Solo. Tormented by the memory of his fled girlfriend Lisa and begged by Solo to end its useless "life", Jimi begins a search for people who can help him both to discover what happened to Lisa and to delete his game before it is released.
 6.4
6.4Hackers(en)
Along with his new friends, a teenager who was arrested by the US Secret Service and banned from using a computer for writing a computer virus discovers a plot by a nefarious hacker, but they must use their computer skills to find the evidence while being pursued by the Secret Service and the evil computer genius behind the virus.
 6.1
6.1Takedown(en)
Kevin Mitnick is quite possibly the best hacker in the world. Hunting for more and more information, seeking more and more cyber-trophies every day, he constantly looks for bigger challenges. When he breaks into the computer of a security expert and an ex-hacker, he finds one - and much more than that...
 6.8
6.8The Italian Job(en)
Charlie Croker pulled off the crime of a lifetime. The one thing that he didn't plan on was being double-crossed. Along with a drop-dead gorgeous safecracker, Croker and his team take off to re-steal the loot and end up in a pulse-pounding, pedal-to-the-metal chase that careens up, down, above and below the streets of Los Angeles.
 6.3
6.3Swordfish(en)
Rogue agent Gabriel Shear is determined to get his mitts on $9 billion stashed in a secret Drug Enforcement Administration account. He wants the cash to fight terrorism, but lacks the computer skills necessary to hack into the government mainframe. Enter Stanley Jobson, a n'er-do-well encryption expert who can log into anything.
 0.0
0.0Hadron(en)
Hacktivists risk it all to uncover the work of an elite branch of government research and technology in this found footage style race to bring darkness to light. How far are you willing to go to expose the truth? It's all speculation..until it's not.
 0.0
0.0Never Saw Me Coming(en)
Described as a heist thriller that becomes “a powerful examination of systemic prejudice and economic inequality,” the stranger-than-fiction story follows Smith’s journey from teenage hacker to financial system mastermind. By 18, she had already orchestrated a litany of heists, amassing millions of dollars while evading law enforcement in the process.
 7.4
7.4Ghost in the Shell: Stand Alone Complex - Solid State Society(ja)
The story takes place in the year 2034, two years after the events in Ghost in the Shell: S.A.C. 2nd GIG. Female cyborg Major Motoko Kusanagi has left Public Security Section 9, an elite counter-terrorist and anti-crime unit specializing in cyber-warfare, which has expanded to a team of 20 field operatives with Togusa acting as the field lead.
 0.0
0.0O Novo Corpo(pt)
On an isolated farm, a woman finds an injured and frightened woman in her old chicken coop. Moved by an inexplicable instinct, she decides to help her, without imagining that this silent encounter will awaken buried secrets. When tension finally gives way to trust, something dark approaches, bringing a truth that no one could have foreseen.
 6.8
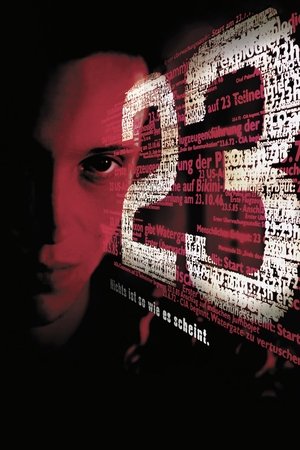
6.823(de)
The movie's plot is based on the true story of a group of young computer hackers from Hannover, Germany. In the late 1980s the orphaned Karl Koch invests his heritage in a flat and a home computer. At first he dials up to bulletin boards to discuss conspiracy theories inspired by his favorite novel, R.A. Wilson's "Illuminatus", but soon he and his friend David start breaking into government and military computers. Pepe, one of Karl's rather criminal acquaintances senses that there is money in computer cracking - he travels to east Berlin and tries to contact the KGB.