
Rats and Slaves(2019)
Nowadays hacking is a well known phenomenon. Almost weekly we see news items about networks that are attacked. The trading of access to ones personal computer and webcam is less widely known, but the results can affect a computer user deeply personal. The simplicity of these hacks and the scale of it are disturbing. Are you already the slave of a RAT, or will you become one very soon?
Movie: Rats and Slaves
Video Trailer Rats and Slaves
Similar Movies
 6.4
6.4In the Realm of the Hackers(en)
In The Realm of the Hackers is a documentary about the prominent hacker community, centered in Melbourne, Australia in the late 80's to early 1990. The storyline is centered around the Australian teenagers going by the hacker names "Electron" and "Phoenix", who were members of an elite computer hacking group called The Realm and hacked into some of the most secure computer networks in the world, including those of the US Naval Research Laboratory, Lawrence Livermore National Laboratory, a government lab charged with the security of the US nuclear stockpile, and NASA.
 0.0
0.0Solid Rock Trust(en)
Armed with only a collection of cell phones and a unique talent, a hacker orchestrates an elaborate bank heist from an abandoned building. But when things spin out of control, she has her wits to hold it all together.
 7.0
7.0The Girl Who Played with Fire(sv)
Mikael Blomkvist, publisher of Millennium magazine, has made his living exposing the crooked and corrupt practices of establishment Swedish figures. So when a young journalist approaches him with a meticulously researched thesis about sex trafficking in Sweden and those in high office who abuse underage girls, Blomkvist immediately throws himself into the investigation.
 4.2
4.2Dot.Kill(en)
Charlie Daines is a morphine-addicted detective on the trail of a psychopath who is setting up murders and broadcasting them live on the internet. As he closes in on the killer, Charlie realises that he is to be the final victim.
 6.8
6.8The Crazy Che(es)
The incredible story of Bill Gaede, an Argentinian engineer, programmer… and Cold War spy.
 6.9
6.9Sneakers(en)
When shadowy U.S. intelligence agents blackmail a reformed computer hacker and his eccentric team of security experts into stealing a code-breaking 'black box' from a Soviet-funded genius, they uncover a bigger conspiracy. Now, he and his 'sneakers' must save themselves and the world economy by retrieving the box from their blackmailers.
 7.0
7.0Freedom Downtime(en)
A feature-length documentary about the Free Kevin movement and the hacker world.
 5.8
5.8Firewall(en)
State-of-the-art security system creator Jack Stanfield has cemented his reputation as a man who's thought of everything. But when a criminal finds a way into his personal life, everything Jack holds dear is suddenly at stake.
 6.8
6.8The Italian Job(en)
Charlie Croker pulled off the crime of a lifetime. The one thing that he didn't plan on was being double-crossed. Along with a drop-dead gorgeous safecracker, Croker and his team take off to re-steal the loot and end up in a pulse-pounding, pedal-to-the-metal chase that careens up, down, above and below the streets of Los Angeles.
 6.3
6.3Swordfish(en)
Rogue agent Gabriel Shear is determined to get his mitts on $9 billion stashed in a secret Drug Enforcement Administration account. He wants the cash to fight terrorism, but lacks the computer skills necessary to hack into the government mainframe. Enter Stanley Jobson, a n'er-do-well encryption expert who can log into anything.
 6.0
6.0Antitrust(en)
A computer programmer's dream job at a hot Portland-based firm turns nightmarish when he discovers his boss has a secret and ruthless means of dispatching anti-trust problems.
 7.5
7.5The Girl with the Dragon Tattoo(sv)
Swedish thriller based on Stieg Larsson's novel about a male journalist and a young female hacker. In the opening of the movie, Mikael Blomkvist, a middle-aged publisher for the magazine Millennium, loses a libel case brought by corrupt Swedish industrialist Hans-Erik Wennerström. Nevertheless, he is hired by Henrik Vanger in order to solve a cold case, the disappearance of Vanger's niece
 7.4
7.4Ghost in the Shell: Stand Alone Complex - Solid State Society(ja)
The story takes place in the year 2034, two years after the events in Ghost in the Shell: S.A.C. 2nd GIG. Female cyborg Major Motoko Kusanagi has left Public Security Section 9, an elite counter-terrorist and anti-crime unit specializing in cyber-warfare, which has expanded to a team of 20 field operatives with Togusa acting as the field lead.
 2.5
2.5Fisher(en)
In the small town of Eden, Tennessee, a neglected and naive teenage girl named Clara Banks has made a habit of deceiving people online for gifts, a gambit known as "catfishing." She thinks it's all fun and games until she hooks the attention of the wrong person. A short time later, events set into motion spiral out of control as someone begins stalking Clara and her friends. As the consequences of her actions return to haunt her, twisted messages start showing up at Clara's home, causing her to fear for her life. Will she ever feel safe again now that the evil has come knocking?
 6.9
6.9Revolution OS(en)
REVOLUTION OS tells the inside story of the hackers who rebelled against the proprietary software model and Microsoft to create GNU/Linux and the Open Source movement.
 7.2
7.2Putin's Bears - The Most Dangerous Hackers in the World(de)
They call themselves Fancy Bear, Cozy Bear or Voodoo Bear. Elite units of the Russian secret services are hidden behind these code names. They are among the most dangerous hackers in the world. The bears were already in the computer of then-Chancellor Angela Merkel in 2015, interfered in the US election campaign in 2016 and are currently influencing the war in Ukraine. The makers of the successful YouTube channel “Simplicissimus” in co-production with funk and SWR are back and show the destructive potential of state hacking with this documentary. With the help of leading German hackers, cyberspace experts and a lot of humor, they delicately demystify the Russian bears: Who are the people behind them? How do they operate? And what makes them so incredibly dangerous?
 8.0
8.0A Dangerous Boy(en)
Sigurdur Thordarson, known as Siggi, becomes a hacker at 12, exposing Icelandic bank corruption at 14. Branded the "teenage whistleblower," he joins WikiLeaks in 2010, mentored by Julian Assange. Siggi leaks globally, but clashes with Assange, prompting him to spy for the FBI at 18. This tale weaves paranoia, hacking, and friendship, portraying Siggi's turbulent journey from trust to betrayal, revealing a heart-wrenching coming-of-age narrative.
 6.4
6.4Hackers(en)
Along with his new friends, a teenager who was arrested by the US Secret Service and banned from using a computer for writing a computer virus discovers a plot by a nefarious hacker, but they must use their computer skills to find the evidence while being pursued by the Secret Service and the evil computer genius behind the virus.
 0.0
0.0Never Saw Me Coming(en)
Described as a heist thriller that becomes “a powerful examination of systemic prejudice and economic inequality,” the stranger-than-fiction story follows Smith’s journey from teenage hacker to financial system mastermind. By 18, she had already orchestrated a litany of heists, amassing millions of dollars while evading law enforcement in the process.
 9.0
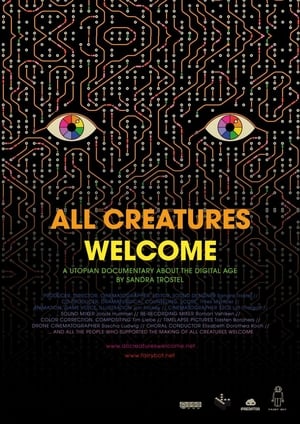
9.0All Creatures Welcome(de)
All Creatures Welcome explores the world of hackers and nerds at the events of the Chaos Computer Club, Europe's largest hacker association. The film dispels common clichés and draws a utopian picture of a possible society in the digital age.

